


In this blog we explain phone fraud possibilities with 2-Factor Authentication. We discussed the basics of Toll Fraud in a previous blog article. Often it is about abusing the victim’s telephone network or subscription to make expensive premium calls from which the revenues flow back to the criminals.
One example is where criminals pay – for example – cleaning staff to dial premium numbers in the evening hours. The only ‘content’ provided via those premium numbers is a standard busy tone. So, when employees arrive the next day, they just find a phone off-hook (perhaps because it has been cleaned or something?). Only weeks later it is discovered that hundreds or even thousands of dollars or euros were charged on a single phone extension for outgoing calls to a premium number. If you multiply that by the number of phone lines involved, we are talking about serious money.
 However, there are many more potential phone fraud scenarios. I couldn’t withhold a smile when I read this example. A security analyst – he reported the bug he found to the relevant bug bounty programs and published it on his blog – found a very easy way to fork over money to his own account using a very common callback mechanism. He tried it with three companies who typically spend some money on IT security. You may have heard their names before: Microsoft, Google, and Instagram.
However, there are many more potential phone fraud scenarios. I couldn’t withhold a smile when I read this example. A security analyst – he reported the bug he found to the relevant bug bounty programs and published it on his blog – found a very easy way to fork over money to his own account using a very common callback mechanism. He tried it with three companies who typically spend some money on IT security. You may have heard their names before: Microsoft, Google, and Instagram.
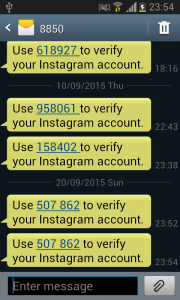
These companies, and they are for sure not the only ones, use for some of their services an authorisation mechanism – the so-called 2-factor authentication – where the user receives a code via a text message which he has to enter in a login screen. However, if the user doesn’t respond to the text message, he receives a call instead. And that is where it becomes interesting. The security analyst found out that he could provide any telephone number for this authentication service, including premium numbers. As a result, the two-factor authentication server itself starts calling a premium number which can charge dollars or euro’s per call. The researcher collected a symbolic dollar from the companies to prove his case and the contacted the three multinationals via their bug bounty programs.
In his blog, he also calculated the potential amount of money which a less honest person could have stolen. By using tricks which are both simple and smart, it is possible to trigger the same premium number call again and again, and he calculated that the potential loss for these companies was in the 6 or 7 digit numbers.
We often get the feedback from people that they consider telephony security as less important compared to ‘common’ ICT security. Looking at examples like the one above, that might not be completely true.